PO9.3:
PO 9.3 Event Identification
Control Objective:
Identify any event (threat and vulnerability) with a potential impact on the goals or operations of the enterprise, including business, regulatory, legal, technology, trading partner, human resources and operational aspects. Determine the nature of the impact— positive, negative or both—and maintain this information.
Applicability:
- Sarbanes-Oxley
- HIPAA
- GLBA
- PCI
- FISMA
- NIST SP 800-66
- Ditscap
- Control Exception
- User Defined
Risk Association Control Activities:
- 1. Risk: Third party service providers may not meet business, compliance and regulatory needs of the business inducing risk.
- a. SOX.1.5 A designated individual is responsible for regular monitoring and reporting on the achievement of the third-party service-level performance criteria.
- a. SOX.1.5 A designated individual is responsible for regular monitoring and reporting on the achievement of the third-party service-level performance criteria.
- 1. Risk: Third party service providers may not meet business, compliance and regulatory needs of the business inducing risk.
- 2. Risk: Users may have inappropriate access to the application system.
- a. SOX.5.1.1 Access to the application system is appropriately restricted to prevent unauthorized activity.
- a. SOX.5.1.1 Access to the application system is appropriately restricted to prevent unauthorized activity.
- 2. Risk: Users may have inappropriate access to the application system.
Implementation Guide:
Process Narrative
Insert a description of the process narration that is applicable to the existing control statement this narrative refers to.
Process Illustration
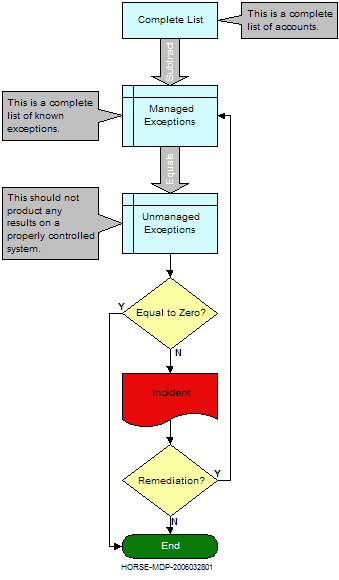
The following illustration depicts the process for identifying access accounts currently on a system and then comparing this list to a control list of exceptions that has been previously certified by management. Any accounts that remain should be investigated as they are most likely policy violations and a breakdown in the segregation of duties has occurred.
Control Commentary
Insert a description of the control that is applicable to the existing control statement this commentary refers to.
Control Exception Commentary
All accounts that remain following the comparison to current system accounts should be investigated as they are most likely policy violations and the result of a breakdown with segregation of duties or possibly an instance of collusion.
Evidence Archive Location
Insert Evidence Description Here.
Control Status and Auditors Commentary
Describe the condition of the applicable control and its effectiveness. Set the color icon to a redlock.jpg, yellowlock.jpg or greenlock.jpg.
File:Redlock.jpg
Remediation Plan
Insert remediation plan, applicability, or any information that indicates what needs to be done.
Supplemental Information:
ITIL Service Delivery, Availability Management.
ITIL 8.9.3 CRAMM.
ISO 17799 4.2 Security of third-party access.
ISO 5.2 Information classification.
ISO 7.1 Secure areas.
ISO 7.2 Equipment security.
ISO 9.2 User access management.
ISO 9.4 Network access control.
ISO 10.3 Cryptographic controls.
Implementation guidance
Insert guidance in this section if it helps to elaborate upon the subject matter. Examples of evidence that would help guide the end user is desirable.