Uncategorized files
Jump to navigation
Jump to search
Showing below up to 100 results in range #51 to #150.
-
Asset Management Standard.png 2,480 × 3,508; 38 KB
-
Asset Protection Standard(1).png 2,480 × 3,508; 50 KB
-
Asset Protection Standard(2).png 2,480 × 3,508; 100 KB
-
Asset Protection Standard(3).png 2,480 × 3,508; 113 KB
-
Asset Protection Standard(4).png 2,480 × 3,508; 107 KB
-
Asset Protection Standard(5).png 2,480 × 3,508; 78 KB
-
Asset Protection Standard(6).png 2,480 × 3,508; 27 KB
-
Asset Protection Standard.png 2,480 × 3,508; 37 KB
-
AuditMachine-AD2014.gif 200 × 200; 81 KB
-
Auditing Standard(1).png 2,480 × 3,508; 50 KB
-
Auditing Standard(2).png 2,480 × 3,508; 76 KB
-
Auditing Standard(3).png 2,480 × 3,508; 59 KB
-
Auditing Standard(4).png 2,480 × 3,508; 64 KB
-
Auditing Standard(5).png 2,480 × 3,508; 110 KB
-
Auditing Standard(6).png 2,480 × 3,508; 60 KB
-
Auditing Standard.png 2,480 × 3,508; 36 KB
-
Availability Protection Standard(1).png 2,480 × 3,508; 50 KB
-
Availability Protection Standard(2).png 2,480 × 3,508; 83 KB
-
Availability Protection Standard(3).png 2,480 × 3,508; 76 KB
-
Availability Protection Standard(4).png 2,480 × 3,508; 78 KB
-
Availability Protection Standard(5).png 2,480 × 3,508; 85 KB
-
Availability Protection Standard(6).png 2,480 × 3,508; 119 KB
-
Availability Protection Standard(7).png 2,480 × 3,508; 39 KB
-
Availability Protection Standard.png 2,480 × 3,508; 38 KB
-
BCP-HORSE-2007053001.jpg 811 × 439; 162 KB
-
BCPLifecycle.gif 220 × 220; 8 KB
-
BYOD Acceptable Use Standard(1).png 2,480 × 3,508; 50 KB
-
BYOD Acceptable Use Standard(10).png 2,480 × 3,508; 32 KB
-
BYOD Acceptable Use Standard(2).png 2,480 × 3,508; 99 KB
-
BYOD Acceptable Use Standard(3).png 2,480 × 3,508; 80 KB
-
BYOD Acceptable Use Standard(4).png 2,480 × 3,508; 77 KB
-
BYOD Acceptable Use Standard(5).png 2,480 × 3,508; 87 KB
-
BYOD Acceptable Use Standard(6).png 2,480 × 3,508; 85 KB
-
BYOD Acceptable Use Standard(7).png 2,480 × 3,508; 74 KB
-
BYOD Acceptable Use Standard(8).png 2,480 × 3,508; 76 KB
-
BYOD Acceptable Use Standard(9).png 2,480 × 3,508; 101 KB
-
BYOD Acceptable Use Standard.png 2,480 × 3,508; 38 KB
-
BackupSystemAudit.txt ; 22 KB
-
BeKnown.jpg 30 × 30; 16 KB
-
Blacklock.png 60 × 60; 3 KB
-
Bluelock.png 60 × 60; 3 KB
-
Business-Case-for-Computer-Forensics.pdf 1,250 × 1,650, 5 pages; 147 KB
-
CFLC-tn.jpg 94 × 140; 15 KB
-
CIRCULAR-NO-A-130.pdf 1,275 × 1,650, 23 pages; 92 KB
-
Cism-mdp-20081.jpg 1,024 × 775; 584 KB
-
Cissp.jpg 75 × 75; 2 KB
-
Classes10.png 491 × 300; 11 KB
-
Computer-Forensics-Laboratory.pdf 1,277 × 1,650, 7 pages; 97 KB
-
Computer-Forensics-Today.pdf 1,250 × 1,650, 5 pages; 77 KB
-
Configuration-management-security.pdf 1,275 × 1,650, 9 pages; 167 KB
-
Configuration Management Standard(1).png 2,480 × 3,508; 50 KB
-
Configuration Management Standard(2).png 2,480 × 3,508; 80 KB
-
Configuration Management Standard(3).png 2,480 × 3,508; 59 KB
-
Configuration Management Standard(4).png 2,480 × 3,508; 73 KB
-
Configuration Management Standard(5).png 2,480 × 3,508; 70 KB
-
Configuration Management Standard(6).png 2,480 × 3,508; 105 KB
-
Configuration Management Standard(7).png 2,480 × 3,508; 101 KB
-
Configuration Management Standard(8).png 2,480 × 3,508; 31 KB
-
Configuration Management Standard.png 2,480 × 3,508; 38 KB
-
Console-access-a.jpg 285 × 361; 41 KB
-
Control Data model.JPG 290 × 193; 8 KB
-
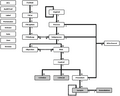
Control Process data model.JPG 577 × 205; 16 KB
-
Control Process model.jpg 274 × 205; 10 KB
-
Cool1.gif 140 × 45; 5 KB
-
DS-A.jpg 810 × 1,028; 355 KB
-
DS-B.jpg 810 × 1,026; 313 KB
-
Database-security-2007020901.png 499 × 616; 24 KB
-
Database-views-2007020901.png 628 × 503; 44 KB
-
Dcid-6-3-manual.pdf 1,275 × 1,650, 156 pages; 435 KB
-
Defamation Comprehensive Review Chart.jpg 3,400 × 2,200; 272 KB
-
Development-of-Information-Classification-Standard.pdf 1,275 × 1,650, 18 pages; 1.27 MB
-
Development-of-Information-Labeling-Standard.pdf 1,275 × 1,650, 15 pages; 299 KB
-
Development-of-Internet-Acceptable-Use-Standards.pdf 1,275 × 1,650, 17 pages; 884 KB
-
Development-of-an-Incident-Response-Standard.pdf 1,275 × 1,650, 18 pages; 1.23 MB
-
Developmental Electronic Mail Acceptable Usage Standard.pdf 1,275 × 1,650, 15 pages; 219 KB
-
E-Government-Act-2002.pdf 1,275 × 1,650, 72 pages; 218 KB
-
Ediscovery-project-manage.pdf 1,275 × 1,650, 11 pages; 334 KB
-
Electronic-access-a.jpg 283 × 361; 38 KB
-
Electronic Mail Acceptable Use Standard(1).png 2,480 × 3,508; 50 KB
-
Electronic Mail Acceptable Use Standard(2).png 2,480 × 3,508; 90 KB
-
Electronic Mail Acceptable Use Standard(3).png 2,480 × 3,508; 91 KB
-
Electronic Mail Acceptable Use Standard(4).png 2,480 × 3,508; 86 KB
-
Electronic Mail Acceptable Use Standard(5).png 2,480 × 3,508; 74 KB
-
Electronic Mail Acceptable Use Standard(6).png 2,480 × 3,508; 91 KB
-
Electronic Mail Acceptable Use Standard(7).png 2,480 × 3,508; 72 KB
-
Electronic Mail Acceptable Use Standard(8).png 2,480 × 3,508; 26 KB
-
Electronic Mail Acceptable Use Standard.png 2,480 × 3,508; 38 KB
-
Employee Ongoing Security Awareness Standard(1).png 2,480 × 3,508; 48 KB
-
Employee Ongoing Security Awareness Standard(2).png 2,480 × 3,508; 86 KB
-
Employee Ongoing Security Awareness Standard(3).png 2,480 × 3,508; 83 KB
-
Employee Ongoing Security Awareness Standard(4).png 2,480 × 3,508; 70 KB
-
Employee Ongoing Security Awareness Standard.png 2,480 × 3,508; 39 KB
-
Encryption Standard(1).png 2,480 × 3,508; 50 KB
-
Encryption Standard(2).png 2,480 × 3,508; 99 KB
-
Encryption Standard(3).png 2,480 × 3,508; 83 KB
-
Encryption Standard(4).png 2,480 × 3,508; 64 KB
-
Encryption Standard(5).png 2,480 × 3,508; 75 KB
-
Encryption Standard(6).png 2,480 × 3,508; 106 KB
-
Encryption Standard(7).png 2,480 × 3,508; 57 KB
-
Encryption Standard.png 2,480 × 3,508; 37 KB