Uncategorized files
Jump to navigation
Jump to search
Showing below up to 349 results in range #1 to #349.
-
0031.pdf 1,275 × 1,650, 34 pages; 392 KB
-
1-Million-Pages2.jpg 600 × 100; 94 KB
-
1DB7A2CDd01.pdf 1,275 × 1,650, 72 pages; 210 KB
-
A8F65d01.pdf 1,275 × 1,650, 6 pages; 343 KB
-
AD-CXO2013012003.gif 160 × 300; 30 KB
-
AD201211060 160x3002.gif 160 × 300; 91 KB
-
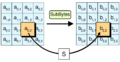
AES-AddRoundKey.png 771 × 600; 80 KB
-
AES-MixColumns.png 800 × 425; 65 KB
-
AES-ShiftRows.png 800 × 296; 64 KB
-
AES-SubBytes.png 800 × 415; 62 KB
-
AI-A.jpg 810 × 1,026; 354 KB
-
Acceptable Use Standard(1).png 2,480 × 3,508; 50 KB
-
Acceptable Use Standard(2).png 2,480 × 3,508; 104 KB
-
Acceptable Use Standard(3).png 2,480 × 3,508; 101 KB
-
Acceptable Use Standard(4).png 2,480 × 3,508; 83 KB
-
Acceptable Use Standard(5).png 2,480 × 3,508; 28 KB
-
Acceptable Use Standard.png 2,480 × 3,508; 37 KB
-
Access Control Standard(1).png 2,480 × 3,508; 50 KB
-
Access Control Standard(10).png 2,480 × 3,508; 26 KB
-
Access Control Standard(2).png 2,480 × 3,508; 101 KB
-
Access Control Standard(3).png 2,480 × 3,508; 70 KB
-
Access Control Standard(4).png 2,480 × 3,508; 77 KB
-
Access Control Standard(5).png 2,480 × 3,508; 76 KB
-
Access Control Standard(6).png 2,480 × 3,508; 79 KB
-
Access Control Standard(7).png 2,480 × 3,508; 78 KB
-
Access Control Standard(8).png 2,480 × 3,508; 123 KB
-
Access Control Standard(9).png 2,480 × 3,508; 74 KB
-
Access Control Standard.png 2,480 × 3,508; 37 KB
-
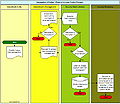
Account-audit-flow.jpg 339 × 580; 49 KB
-
AlternateExceptionHandling.jpg 422 × 468; 24 KB
-
Amazon.jpg 30 × 30; 10 KB
-
Anti-Virus Standard(1).png 2,480 × 3,508; 50 KB
-
Anti-Virus Standard(2).png 2,480 × 3,508; 91 KB
-
Anti-Virus Standard(3).png 2,480 × 3,508; 86 KB
-
Anti-Virus Standard(4).png 2,480 × 3,508; 85 KB
-
Anti-Virus Standard(5).png 2,480 × 3,508; 84 KB
-
Anti-Virus Standard(6).png 2,480 × 3,508; 117 KB
-
Anti-Virus Standard(7).png 2,480 × 3,508; 44 KB
-
Anti-Virus Standard.png 2,480 × 3,508; 37 KB
-
Asset Identification and Classification Standard(1).png 2,480 × 3,508; 50 KB
-
Asset Identification and Classification Standard(2).png 2,480 × 3,508; 109 KB
-
Asset Identification and Classification Standard(3).png 2,480 × 3,508; 104 KB
-
Asset Identification and Classification Standard(4).png 2,480 × 3,508; 87 KB
-
Asset Identification and Classification Standard(5).png 2,480 × 3,508; 28 KB
-
Asset Identification and Classification Standard.png 2,480 × 3,508; 38 KB
-
Asset Management Standard(1).png 2,480 × 3,508; 50 KB
-
Asset Management Standard(2).png 2,480 × 3,508; 105 KB
-
Asset Management Standard(3).png 2,480 × 3,508; 103 KB
-
Asset Management Standard(4).png 2,480 × 3,508; 78 KB
-
Asset Management Standard(5).png 2,480 × 3,508; 27 KB
-
Asset Management Standard.png 2,480 × 3,508; 38 KB
-
Asset Protection Standard(1).png 2,480 × 3,508; 50 KB
-
Asset Protection Standard(2).png 2,480 × 3,508; 100 KB
-
Asset Protection Standard(3).png 2,480 × 3,508; 113 KB
-
Asset Protection Standard(4).png 2,480 × 3,508; 107 KB
-
Asset Protection Standard(5).png 2,480 × 3,508; 78 KB
-
Asset Protection Standard(6).png 2,480 × 3,508; 27 KB
-
Asset Protection Standard.png 2,480 × 3,508; 37 KB
-
AuditMachine-AD2014.gif 200 × 200; 81 KB
-
Auditing Standard(1).png 2,480 × 3,508; 50 KB
-
Auditing Standard(2).png 2,480 × 3,508; 76 KB
-
Auditing Standard(3).png 2,480 × 3,508; 59 KB
-
Auditing Standard(4).png 2,480 × 3,508; 64 KB
-
Auditing Standard(5).png 2,480 × 3,508; 110 KB
-
Auditing Standard(6).png 2,480 × 3,508; 60 KB
-
Auditing Standard.png 2,480 × 3,508; 36 KB
-
Availability Protection Standard(1).png 2,480 × 3,508; 50 KB
-
Availability Protection Standard(2).png 2,480 × 3,508; 83 KB
-
Availability Protection Standard(3).png 2,480 × 3,508; 76 KB
-
Availability Protection Standard(4).png 2,480 × 3,508; 78 KB
-
Availability Protection Standard(5).png 2,480 × 3,508; 85 KB
-
Availability Protection Standard(6).png 2,480 × 3,508; 119 KB
-
Availability Protection Standard(7).png 2,480 × 3,508; 39 KB
-
Availability Protection Standard.png 2,480 × 3,508; 38 KB
-
BCP-HORSE-2007053001.jpg 811 × 439; 162 KB
-
BCPLifecycle.gif 220 × 220; 8 KB
-
BYOD Acceptable Use Standard(1).png 2,480 × 3,508; 50 KB
-
BYOD Acceptable Use Standard(10).png 2,480 × 3,508; 32 KB
-
BYOD Acceptable Use Standard(2).png 2,480 × 3,508; 99 KB
-
BYOD Acceptable Use Standard(3).png 2,480 × 3,508; 80 KB
-
BYOD Acceptable Use Standard(4).png 2,480 × 3,508; 77 KB
-
BYOD Acceptable Use Standard(5).png 2,480 × 3,508; 87 KB
-
BYOD Acceptable Use Standard(6).png 2,480 × 3,508; 85 KB
-
BYOD Acceptable Use Standard(7).png 2,480 × 3,508; 74 KB
-
BYOD Acceptable Use Standard(8).png 2,480 × 3,508; 76 KB
-
BYOD Acceptable Use Standard(9).png 2,480 × 3,508; 101 KB
-
BYOD Acceptable Use Standard.png 2,480 × 3,508; 38 KB
-
BackupSystemAudit.txt ; 22 KB
-
BeKnown.jpg 30 × 30; 16 KB
-
Blacklock.png 60 × 60; 3 KB
-
Bluelock.png 60 × 60; 3 KB
-
Business-Case-for-Computer-Forensics.pdf 1,250 × 1,650, 5 pages; 147 KB
-
CFLC-tn.jpg 94 × 140; 15 KB
-
CIRCULAR-NO-A-130.pdf 1,275 × 1,650, 23 pages; 92 KB
-
Cism-mdp-20081.jpg 1,024 × 775; 584 KB
-
Cissp.jpg 75 × 75; 2 KB
-
Classes10.png 491 × 300; 11 KB
-
Computer-Forensics-Laboratory.pdf 1,277 × 1,650, 7 pages; 97 KB
-
Computer-Forensics-Today.pdf 1,250 × 1,650, 5 pages; 77 KB
-
Configuration-management-security.pdf 1,275 × 1,650, 9 pages; 167 KB
-
Configuration Management Standard(1).png 2,480 × 3,508; 50 KB
-
Configuration Management Standard(2).png 2,480 × 3,508; 80 KB
-
Configuration Management Standard(3).png 2,480 × 3,508; 59 KB
-
Configuration Management Standard(4).png 2,480 × 3,508; 73 KB
-
Configuration Management Standard(5).png 2,480 × 3,508; 70 KB
-
Configuration Management Standard(6).png 2,480 × 3,508; 105 KB
-
Configuration Management Standard(7).png 2,480 × 3,508; 101 KB
-
Configuration Management Standard(8).png 2,480 × 3,508; 31 KB
-
Configuration Management Standard.png 2,480 × 3,508; 38 KB
-
Console-access-a.jpg 285 × 361; 41 KB
-
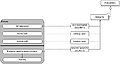
Control Data model.JPG 290 × 193; 8 KB
-
Control Process data model.JPG 577 × 205; 16 KB
-
Control Process model.jpg 274 × 205; 10 KB
-
Cool1.gif 140 × 45; 5 KB
-
DS-A.jpg 810 × 1,028; 355 KB
-
DS-B.jpg 810 × 1,026; 313 KB
-
Database-security-2007020901.png 499 × 616; 24 KB
-
Database-views-2007020901.png 628 × 503; 44 KB
-
Dcid-6-3-manual.pdf 1,275 × 1,650, 156 pages; 435 KB
-
Defamation Comprehensive Review Chart.jpg 3,400 × 2,200; 272 KB
-
Development-of-Information-Classification-Standard.pdf 1,275 × 1,650, 18 pages; 1.27 MB
-
Development-of-Information-Labeling-Standard.pdf 1,275 × 1,650, 15 pages; 299 KB
-
Development-of-Internet-Acceptable-Use-Standards.pdf 1,275 × 1,650, 17 pages; 884 KB
-
Development-of-an-Incident-Response-Standard.pdf 1,275 × 1,650, 18 pages; 1.23 MB
-
Developmental Electronic Mail Acceptable Usage Standard.pdf 1,275 × 1,650, 15 pages; 219 KB
-
E-Government-Act-2002.pdf 1,275 × 1,650, 72 pages; 218 KB
-
Ediscovery-project-manage.pdf 1,275 × 1,650, 11 pages; 334 KB
-
Electronic-access-a.jpg 283 × 361; 38 KB
-
Electronic Mail Acceptable Use Standard(1).png 2,480 × 3,508; 50 KB
-
Electronic Mail Acceptable Use Standard(2).png 2,480 × 3,508; 90 KB
-
Electronic Mail Acceptable Use Standard(3).png 2,480 × 3,508; 91 KB
-
Electronic Mail Acceptable Use Standard(4).png 2,480 × 3,508; 86 KB
-
Electronic Mail Acceptable Use Standard(5).png 2,480 × 3,508; 74 KB
-
Electronic Mail Acceptable Use Standard(6).png 2,480 × 3,508; 91 KB
-
Electronic Mail Acceptable Use Standard(7).png 2,480 × 3,508; 72 KB
-
Electronic Mail Acceptable Use Standard(8).png 2,480 × 3,508; 26 KB
-
Electronic Mail Acceptable Use Standard.png 2,480 × 3,508; 38 KB
-
Employee Ongoing Security Awareness Standard(1).png 2,480 × 3,508; 48 KB
-
Employee Ongoing Security Awareness Standard(2).png 2,480 × 3,508; 86 KB
-
Employee Ongoing Security Awareness Standard(3).png 2,480 × 3,508; 83 KB
-
Employee Ongoing Security Awareness Standard(4).png 2,480 × 3,508; 70 KB
-
Employee Ongoing Security Awareness Standard.png 2,480 × 3,508; 39 KB
-
Encryption Standard(1).png 2,480 × 3,508; 50 KB
-
Encryption Standard(2).png 2,480 × 3,508; 99 KB
-
Encryption Standard(3).png 2,480 × 3,508; 83 KB
-
Encryption Standard(4).png 2,480 × 3,508; 64 KB
-
Encryption Standard(5).png 2,480 × 3,508; 75 KB
-
Encryption Standard(6).png 2,480 × 3,508; 106 KB
-
Encryption Standard(7).png 2,480 × 3,508; 57 KB
-
Encryption Standard.png 2,480 × 3,508; 37 KB
-
End User Computing and Technology Policy(1).png 2,480 × 3,508; 48 KB
-
End User Computing and Technology Policy(2).png 2,480 × 3,508; 98 KB
-
End User Computing and Technology Policy(3).png 2,480 × 3,508; 97 KB
-
End User Computing and Technology Policy(4).png 2,480 × 3,508; 105 KB
-
End User Computing and Technology Policy(5).png 2,480 × 3,508; 45 KB
-
End User Computing and Technology Policy.png 2,480 × 3,508; 38 KB
-
Evaluation process data model.jpg 745 × 395; 29 KB
-
FERPA.pdf 1,275 × 1,650, 51 pages; 296 KB
-
FIPS199.pdf 1,275 × 1,650, 13 pages; 86 KB
-
FIPS200.pdf 1,275 × 1,650, 17 pages; 199 KB
-
Facebook.png 30 × 30; 4 KB
-
Fast-Track-to-Internet-Security.pdf 1,275 × 1,650, 7 pages; 1.26 MB
-
Feedburner.jpg 30 × 30; 2 KB
-
Feedburners.jpg 30 × 30; 2 KB
-
Final Privacy Rule Regulations.pdf 1,275 × 1,650, 55 pages; 2.79 MB
-
Goldseal4.jpg 125 × 125; 20 KB
-
Greenlock.png 60 × 60; 3 KB
-
HORSE-BOOK-V1-TN.jpg 108 × 140; 19 KB
-
HORSE-BOOK-V1.jpg 619 × 806; 290 KB
-
HORSE-COSO-COBIT-X2.jpg 769 × 1,008; 325 KB
-
HORSE-ITAM01-464x600.png 464 × 600; 55 KB
-
HORSE-MECH.png 464 × 600; 55 KB
-
HORSE-SystemWizard-2006.jpg 772 × 938; 28 KB
-
HORSE-SystemWizard-A.jpg 769 × 1,008; 352 KB
-
HORSE-document-heirarchy-2007.jpg 1,825 × 519; 267 KB
-
HORSE-document-heirarchy.jpg 1,034 × 1,010; 387 KB
-
High-risk.jpg 127 × 24; 27 KB
-
Horse-100-wikians-tn.jpg 150 × 150; 50 KB
-
Horse-rodeo.jpg 85 × 90; 12 KB
-
How-To-Spend-a-Dollar-on-Security.pdf 1,275 × 1,650, 3 pages; 39 KB
-
ID-Theft-MDP-2006090101.ppt ; 466 KB
-
ITAM-Mechanized-HORSEPROJECT.png 1,275 × 1,650; 231 KB
-
ITRM-Lifecycle.jpg 960 × 720; 23 KB
-
Image-AES-SubBytes.png 800 × 415; 62 KB
-
Implementation process data model.jpg 757 × 361; 35 KB
-
Incident Response Standard(1).png 2,480 × 3,508; 48 KB
-
Incident Response Standard(2).png 2,480 × 3,508; 90 KB
-
Incident Response Standard(3).png 2,480 × 3,508; 79 KB
-
Incident Response Standard(4).png 2,480 × 3,508; 67 KB
-
Incident Response Standard(5).png 2,480 × 3,508; 80 KB
-
Incident Response Standard(6).png 2,480 × 3,508; 124 KB
-
Incident Response Standard(7).png 2,480 × 3,508; 87 KB
-
Incident Response Standard(8).png 2,480 × 3,508; 28 KB
-
Incident Response Standard.png 2,480 × 3,508; 37 KB
-
Indeed.jpg 30 × 30; 10 KB
-
Information-Security-Policy-Framework-Research-Report.pdf 1,275 × 1,650, 71 pages; 1.09 MB
-
Information Classification Standard(1).png 2,480 × 3,508; 50 KB
-
Information Classification Standard(2).png 2,480 × 3,508; 97 KB
-
Information Classification Standard(3).png 2,480 × 3,508; 73 KB
-
Information Classification Standard(4).png 2,480 × 3,508; 82 KB
-
Information Classification Standard(5).png 2,480 × 3,508; 83 KB
-
Information Classification Standard(6).png 2,480 × 3,508; 118 KB
-
Information Classification Standard(7).png 2,480 × 3,508; 67 KB
-
Information Classification Standard.png 2,480 × 3,508; 38 KB
-
Information Handling Standard(1).png 2,480 × 3,508; 50 KB
-
Information Handling Standard(2).png 2,480 × 3,508; 77 KB
-
Information Handling Standard(3).png 2,480 × 3,508; 54 KB
-
Information Handling Standard(4).png 2,480 × 3,508; 88 KB
-
Information Handling Standard(5).png 2,480 × 3,508; 116 KB
-
Information Handling Standard(6).png 2,480 × 3,508; 73 KB
-
Information Handling Standard(7).png 2,480 × 3,508; 43 KB
-
Information Handling Standard(8).png 2,480 × 3,508; 73 KB
-
Information Handling Standard(9).png 2,480 × 3,508; 39 KB
-
Information Handling Standard.png 2,480 × 3,508; 37 KB
-
Information Labeling Standard(1).png 2,480 × 3,508; 50 KB
-
Information Labeling Standard(2).png 2,480 × 3,508; 89 KB
-
Information Labeling Standard(3).png 2,480 × 3,508; 64 KB
-
Information Labeling Standard(4).png 2,480 × 3,508; 121 KB
-
Information Labeling Standard(5).png 2,480 × 3,508; 66 KB
-
Information Labeling Standard.png 2,480 × 3,508; 37 KB
-
Information Risk Guide.pdf 1,275 × 1,650, 7 pages; 107 KB
-
Information Security Program Charter(1).png 2,480 × 3,508; 50 KB
-
Information Security Program Charter(2).png 2,480 × 3,508; 112 KB
-
Information Security Program Charter(3).png 2,480 × 3,508; 121 KB
-
Information Security Program Charter(4).png 2,480 × 3,508; 82 KB
-
Information Security Program Charter.png 2,480 × 3,508; 38 KB
-
Information Systems and Technology Security Policy(1).png 2,480 × 3,508; 50 KB
-
Information Systems and Technology Security Policy(2).png 2,480 × 3,508; 99 KB
-
Information Systems and Technology Security Policy(3).png 2,480 × 3,508; 91 KB
-
Information Systems and Technology Security Policy(4).png 2,480 × 3,508; 106 KB
-
Information Systems and Technology Security Policy(5).png 2,480 × 3,508; 72 KB
-
Information Systems and Technology Security Policy.png 2,480 × 3,508; 36 KB
-
Intelligent-File-Transfer.pdf 1,275 × 1,650, 11 pages; 203 KB
-
Intentional Torts Comprehensive Review Chart.jpg 3,400 × 2,200; 295 KB
-
Issa-logo.jpg 110 × 110; 30 KB
-
JAFAN 6 3.pdf 1,275 × 1,650, 162 pages; 1.28 MB
-
KY DOI.doc ; 396 KB
-
Key-conrol.jpg 50 × 50; 29 KB
-
Key-control.jpg 50 × 50; 29 KB
-
Lazarus-alliance-red-lock-2013040501-100x100.png 100 × 100; 12 KB
-
Linkedin.jpg 125 × 33; 5 KB
-
Linkedin2.png 30 × 30; 4 KB
-
Low-risk.jpg 127 × 24; 25 KB
-
MDP-2008-headshot01tn.jpg 100 × 132; 18 KB
-
ME-A.jpg 810 × 1,026; 240 KB
-
MOF-all.gif 543 × 451; 47 KB
-
Maintenance process data model.jpg 734 × 277; 27 KB
-
Mba-mdp.jpg 800 × 596; 224 KB
-
Medium-risk.jpg 127 × 24; 26 KB
-
Michael-2010010102.jpg 275 × 200; 26 KB
-
MichaelPeters-Profile201204tn.jpg 200 × 200; 24 KB
-
Michaelpeters org.jpg 30 × 30; 2 KB
-
MiniKit-Computer-Forensic-Tookit.pdf 1,275 × 1,650, 12 pages; 1.27 MB
-
MySQL-CHROOT.txt ; 686 bytes
-
NISTSP800-30.pdf 1,275 × 1,650, 55 pages; 478 KB
-
NISTSP800-37.pdf 1,275 × 1,650, 93 pages; 474 KB
-
NISTSP800-39.pdf 1,275 × 1,650, 67 pages; 538 KB
-
NISTSP800-53.pdf 1,275 × 1,650, 237 pages; 1.21 MB
-
NISTSP800-53A.pdf 1,275 × 1,650, 381 pages; 2.31 MB
-
NISTSP800-59.pdf 1,275 × 1,650, 21 pages; 96 KB
-
NISTSP800-60.pdf 1,275 × 1,650, 53 pages; 401 KB
-
Negligence Comprehensive Review Chart.jpg 3,400 × 2,200; 243 KB
-
Number 7.jpg 85 × 83; 9 KB
-
Nuvola apps knewsticker.png 128 × 128; 17 KB
-
Nuvola apps package editors.png 128 × 128; 21 KB
-
Oracle Audit UNIX Script.txt ; 26 KB
-
PASSWORD FUNCTION.doc ; 29 KB
-
PCI-DSS-V3-CardFlow.png 651 × 975; 89 KB
-
PKI-Primer.pdf 1,275 × 1,650, 15 pages; 322 KB
-
PO-A.jpg 810 × 1,026; 355 KB
-
PO-B.jpg 810 × 1,026; 239 KB
-
PaperworkReductionAct1995.pdf 1,275 × 1,650, 23 pages; 79 KB
-
Personal-CISO.jpg 100 × 100; 25 KB
-
Personal-CXO-Wiki-Featured-sm-tn.jpg 100 × 100; 12 KB
-
Personal-CXO-Wiki-Featured-sm.jpg 170 × 170; 21 KB
-
Physical-access-process.jpg 710 × 618; 134 KB
-
Plan process data model.jpg 626 × 253; 24 KB
-
Policymachine-170x170.png 170 × 170; 32 KB
-
Poolball5.jpg 100 × 101; 20 KB
-
Poolball6.jpg 100 × 100; 24 KB
-
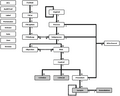
Process data model security management.jpg 820 × 1,309; 143 KB
-
Pysical-access-a.jpg 246 × 361; 33 KB
-
Records-Management.pdf 1,275 × 1,650, 22 pages; 468 KB
-
RedBlack.png 300 × 97; 19 KB
-
Redhorse.jpg 85 × 97; 9 KB
-
Redhorse.png 150 × 172; 13 KB
-
Redlock.png 60 × 60; 3 KB
-
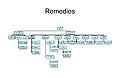
Remedies Comprehensive Review Chart.jpg 3,400 × 2,200; 249 KB
-
Risk-Calculator-Flowchart-Generic-MDP-2013122401.jpg 734 × 1,050; 142 KB
-
Risk-mangement-ALE-2012071501.jpg 939 × 83; 42 KB
-
Risk-mangement-core-2012071501.jpg 705 × 507; 140 KB
-
Risk-mangement-cpm-model-2012071501.jpg 915 × 315; 97 KB
-
Risk-mangement-impact-2012071501.jpg 939 × 291; 158 KB
-
Risk-mangement-impact-analysis-2012071501.jpg 939 × 411; 280 KB
-
Risk-mangement-probability-2012071501.jpg 939 × 231; 116 KB
-
Risk.jpg 362 × 332; 18 KB
-
Risky Business IT security risk management demystified.pdf 1,197 × 1,729, 8 pages; 792 KB
-
SCM activities2.png 750 × 193; 16 KB
-
SCM activity2.PNG 759 × 1,007; 139 KB
-
SCM concepts2.PNG 759 × 1,041; 150 KB
-
SCM example.png 833 × 493; 12 KB
-
SCM model2.png 758 × 1,087; 142 KB
-
Safetynet-green-partner.jpg 100 × 100; 17 KB
-
Safetynet-masthead.jpg 293 × 63; 62 KB
-
Schematic ITSC and RTO, RPO, MI.jpg 1,020 × 250; 47 KB
-
Scsa.jpg 128 × 89; 3 KB
-
Secure-E-Commerce-Applications.pdf 1,275 × 1,650, 77 pages; 1.48 MB
-
Secure-System-Development-Life-Cycle.pdf 1,275 × 1,650, 48 pages; 708 KB
-
Secure-Systems-Architecture-Research-Report.pdf 1,275 × 1,650, 49 pages; 2.78 MB
-
Secure-Your-Database.pdf 1,200 × 1,631, 5 pages; 208 KB
-
Security-Incident-Response-Team-(SIRT)-Development.pdf 1,275 × 1,650, 34 pages; 345 KB
-
Security Awareness Standard(1).png 2,480 × 3,508; 48 KB
-
Security Awareness Standard(2).png 2,480 × 3,508; 104 KB
-
Security Awareness Standard(3).png 2,480 × 3,508; 109 KB
-
Security Awareness Standard(4).png 2,480 × 3,508; 68 KB
-
Security Awareness Standard.png 2,480 × 3,508; 37 KB
-
Servicenet-safetynet-83x83.jpg 83 × 83; 5 KB
-
Session-management-security.pdf 1,168 × 1,579, 3 pages; 454 KB
-
Simple-ethereal-analysis.pdf 1,275 × 1,650, 17 pages; 798 KB
-
Speedo1.jpg 75 × 75; 3 KB
-
Speedo2.jpg 96 × 96; 23 KB
-
Strict Liability Comprehensive Review Chart.jpg 3,400 × 2,200; 230 KB
-
Sy00250 .jpg 75 × 69; 3 KB
-
Technorati.png 30 × 30; 4 KB
-
Termination-process.jpg 710 × 647; 150 KB
-
Threat Assessment and Monitoring Standard(1).png 2,480 × 3,508; 49 KB
-
Threat Assessment and Monitoring Standard(2).png 2,480 × 3,508; 100 KB
-
Threat Assessment and Monitoring Standard(3).png 2,480 × 3,508; 98 KB
-
Threat Assessment and Monitoring Standard(4).png 2,480 × 3,508; 80 KB
-
Threat Assessment and Monitoring Standard(5).png 2,480 × 3,508; 28 KB
-
Threat Assessment and Monitoring Standard.png 2,480 × 3,508; 38 KB
-
Turn2.jpg 96 × 89; 13 KB
-
Turn3.jpg 96 × 96; 23 KB
-
Turn4.jpg 91 × 89; 4 KB
-
Twitter.png 30 × 30; 4 KB
-
Usecase img07.png 653 × 296; 18 KB
-
Very simple sequence.png 210 × 153; 3 KB
-
Vm whatis2.gif 397 × 145; 4 KB
-
Vulnerability Assessment and Management Standard(1).png 2,480 × 3,508; 50 KB
-
Vulnerability Assessment and Management Standard(2).png 2,480 × 3,508; 101 KB
-
Vulnerability Assessment and Management Standard(3).png 2,480 × 3,508; 101 KB
-
Vulnerability Assessment and Management Standard(4).png 2,480 × 3,508; 49 KB
-
Vulnerability Assessment and Management Standard.png 2,480 × 3,508; 39 KB
-
Wipo-copyright.pdf 856 × 1,239, 24 pages; 523 KB
-
Wipo-expression.pdf 875 × 1,235, 26 pages; 207 KB
-
Wipo-industrial.pdf 875 × 1,239, 22 pages; 103 KB
-
Wipo-traditional.pdf 875 × 1,239, 35 pages; 285 KB
-
Wrench.jpg 100 × 67; 4 KB
-
Yellowlock.png 60 × 60; 3 KB