Uploads by Mdpeters
Jump to navigation
Jump to search
This special page shows all uploaded files.
| Date | Name | Thumbnail | Size | Description | Versions |
|---|---|---|---|---|---|
| 09:51, 28 July 2012 | Goldseal4.jpg (file) |  |
20 KB | 2 | |
| 13:56, 21 July 2012 | Nuvola apps package editors.png (file) |  |
21 KB | 2 | |
| 21:14, 6 January 2013 | Personal-CXO-Wiki-Featured-sm.jpg (file) |  |
21 KB | 1 | |
| 10:00, 28 July 2012 | BackupSystemAudit.txt (file) | 22 KB | 2 | ||
| 16:59, 20 July 2012 | ITRM-Lifecycle.jpg (file) |  |
23 KB | 2 | |
| 11:16, 21 July 2012 | Speedo2.jpg (file) |  |
23 KB | 2 | |
| 11:16, 21 July 2012 | Turn3.jpg (file) |  |
23 KB | 2 | |
| 16:12, 20 July 2012 | Poolball6.jpg (file) |  |
24 KB | 2 | |
| 23:47, 21 July 2012 | AlternateExceptionHandling.jpg (file) |  |
24 KB | 2 | |
| 13:56, 21 July 2012 | Database-security-2007020901.png (file) |  |
24 KB | 2 | |
| 13:48, 21 July 2012 | Plan process data model.jpg (file) |  |
24 KB | 2 | |
| 20:30, 12 October 2014 | MichaelPeters-Profile201204tn.jpg (file) |  |
24 KB | 1 | |
| 20:47, 19 July 2012 | Personal-CISO.jpg (file) |  |
25 KB | 6 | |
| 14:53, 20 July 2012 | Low-risk.jpg (file) | 25 KB | 2 | ||
| 17:55, 15 January 2014 | Access Control Standard(10).png (file) |  |
26 KB | 1 | |
| 19:33, 16 January 2014 | Electronic Mail Acceptable Use Standard(8).png (file) |  |
26 KB | 1 | |
| 12:08, 21 July 2012 | Michael-2010010102.jpg (file) |  |
26 KB | 3 | |
| 14:53, 20 July 2012 | Medium-risk.jpg (file) | 26 KB | 2 | ||
| 09:59, 28 July 2012 | Oracle Audit UNIX Script.txt (file) | 26 KB | 2 | ||
| 19:42, 13 January 2014 | Asset Protection Standard(6).png (file) |  |
27 KB | 1 | |
| 14:54, 20 July 2012 | High-risk.jpg (file) | 27 KB | 2 | ||
| 11:08, 21 July 2012 | Maintenance process data model.jpg (file) |  |
27 KB | 2 | |
| 19:53, 13 January 2014 | Asset Management Standard(5).png (file) |  |
27 KB | 1 | |
| 15:24, 21 January 2014 | Incident Response Standard(8).png (file) |  |
28 KB | 1 | |
| 11:59, 29 April 2006 | HORSE-SystemWizard-2006.jpg (file) | Error creating thumbnail: File missing |
28 KB | 1 | |
| 17:48, 14 January 2014 | Acceptable Use Standard(5).png (file) |  |
28 KB | 1 | |
| 19:25, 14 January 2014 | Threat Assessment and Monitoring Standard(5).png (file) |  |
28 KB | 1 | |
| 12:27, 13 January 2014 | Asset Identification and Classification Standard(5).png (file) |  |
28 KB | 1 | |
| 13:58, 21 July 2012 | PASSWORD FUNCTION.doc (file) | 29 KB | 2 | ||
| 23:40, 21 July 2012 | Key-conrol.jpg (file) |  |
29 KB | 2 | |
| 14:46, 20 July 2012 | Key-control.jpg (file) |  |
29 KB | 2 | |
| 11:07, 21 July 2012 | Evaluation process data model.jpg (file) | 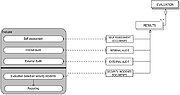 |
29 KB | 2 | |
| 23:42, 21 July 2012 | Issa-logo.jpg (file) |  |
30 KB | 3 | |
| 19:42, 10 September 2013 | AD-CXO2013012003.gif (file) |  |
30 KB | 1 | |
| 21:53, 15 January 2014 | Configuration Management Standard(8).png (file) |  |
31 KB | 1 | |
| 11:35, 30 May 2015 | Policymachine-170x170.png (file) |  |
32 KB | 1 | |
| 18:15, 14 January 2014 | BYOD Acceptable Use Standard(10).png (file) |  |
32 KB | 1 | |
| 23:46, 21 July 2012 | Pysical-access-a.jpg (file) | 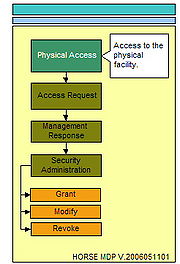 |
33 KB | 2 | |
| 11:08, 21 July 2012 | Implementation process data model.jpg (file) |  |
35 KB | 2 | |
| 15:32, 13 January 2014 | Information Systems and Technology Security Policy.png (file) |  |
36 KB | 1 | |
| 20:10, 15 January 2014 | Auditing Standard.png (file) |  |
36 KB | 1 | |
| 18:14, 23 January 2014 | Information Handling Standard.png (file) |  |
37 KB | 1 | |
| 19:57, 15 January 2014 | Anti-Virus Standard.png (file) |  |
37 KB | 1 | |
| 15:08, 21 January 2014 | Encryption Standard.png (file) |  |
37 KB | 1 | |
| 15:20, 21 January 2014 | Incident Response Standard.png (file) |  |
37 KB | 1 | |
| 19:51, 14 January 2014 | Security Awareness Standard.png (file) |  |
37 KB | 1 | |
| 16:29, 24 September 2014 | Information Labeling Standard.png (file) |  |
37 KB | 1 | |
| 19:40, 13 January 2014 | Asset Protection Standard.png (file) |  |
37 KB | 1 | |
| 17:45, 14 January 2014 | Acceptable Use Standard.png (file) |  |
37 KB | 1 | |
| 17:51, 15 January 2014 | Access Control Standard.png (file) |  |
37 KB | 1 |