PO7.8:
PO 7.8 Job Change and Termination
Control Objective:
Take expedient actions regarding job changes, especially job terminations. Knowledge transfer needs to be arranged, responsibilities reassigned and access rights removed such that risks are minimized and continuity of the function is guaranteed.
Applicability:
- Sarbanes-Oxley
- HIPAA
- GLBA
- PCI
- FISMA
- NIST SP 800-66
- Ditscap
- Control Exception
- User Defined
Risk Association Control Activities:
- 1. Risk: Terminated entities create unacceptable control risks to the Company.
- a. SOX.3.1.4: Management ensures that authorized access to corporate resources terminated entities once possessed has been expeditiously removed.
- a. SOX.3.1.4: Management ensures that authorized access to corporate resources terminated entities once possessed has been expeditiously removed.
- 1. Risk: Terminated entities create unacceptable control risks to the Company.
Implementation Guide:
Process Narrative
Insert a description of the process narration that is applicable to the existing control statement this narrative refers to.
Process Illustration
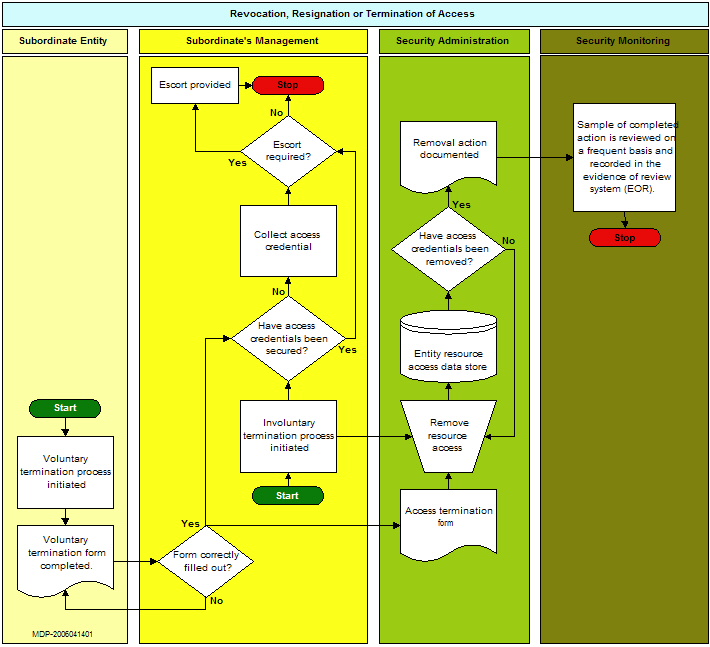
The following illustration represents the business process involved with the removal of access credentials from any system or facility. The catalyst for this removal process would be a voluntary termination or an involuntary termination. The subsequent steps involve the removal of both the individual and the associated access once authorized but now revoked.
Control Commentary
Insert a description of the control that is applicable to the existing control statement this commentary refers to.
Control Exception Commentary
Insert a description of the control exception that is applicable to the existing control statement this commentary refers to.
Evidence Archive Location
Insert Evidence Description Here.
Control Status and Auditors Commentary
Describe the condition of the applicable control and its effectiveness. Set the color icon to a redlock.jpg, yellowlock.jpg or greenlock.jpg.
File:Redlock.jpg
Remediation Plan
Insert remediation plan, applicability, or any information that indicates what needs to be done.
Supplemental Information:
ISO 17799 9.2 User access management.
ISO 6.1 Security in job definition and resource.
Implementation guidance
Insert guidance in this section if it helps to elaborate upon the subject matter. Examples of evidence that would help guide the end user is desirable.